Hello. This is my first post to this blog.
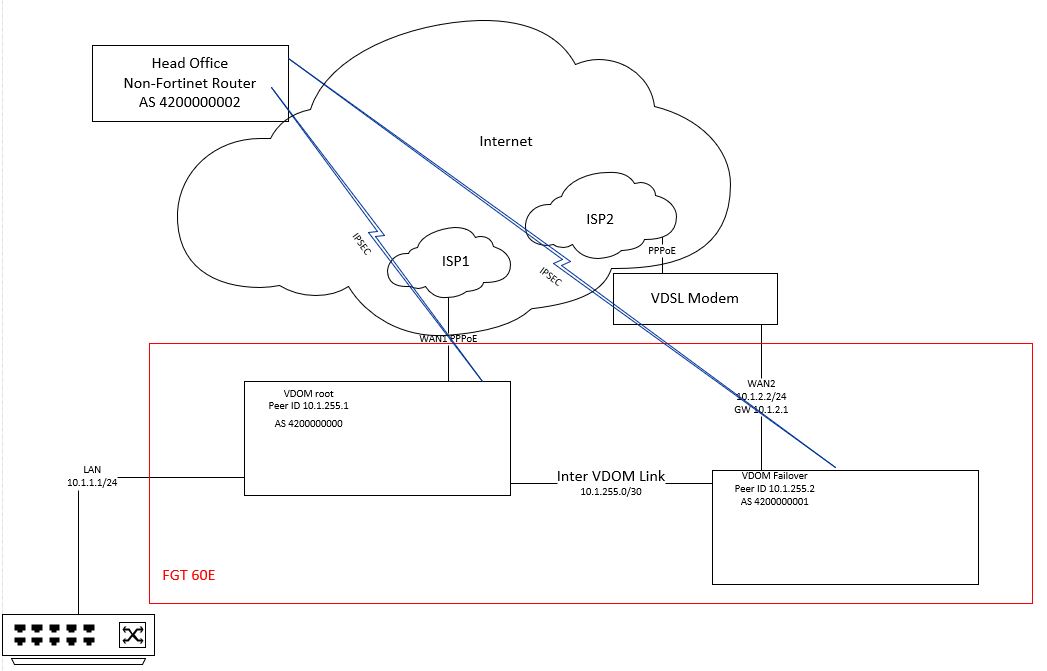
My situation: I have a Fortigate 60E running FortiOS 5.6.3 which is split into 2 VDOMs.
The root VDOM is connected to the Internet via a fast fibre connection while the Failover VDOM is connected via a slower VDSL. Each VDOM has an IPSEC tunnel established to a head office site and are both BGP neighbours with the head office. The VDOMs are also BGP neighbours over a VDOM link:
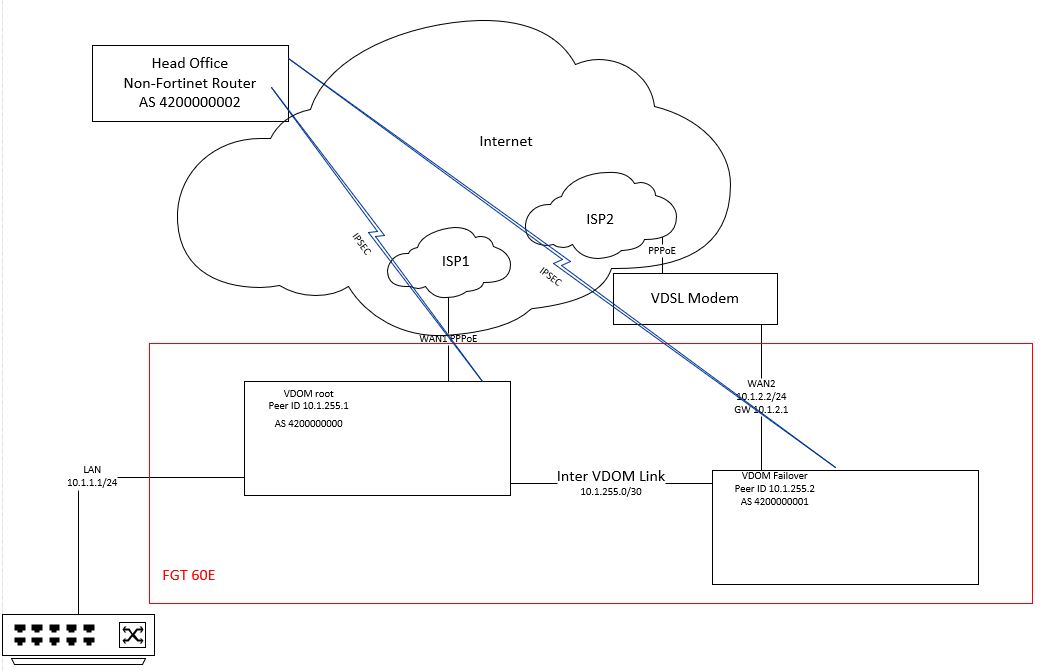
This is all pretty straight forward stuff but I wanted to block certain subnets from being advertised across the VDOM link and also down the IPSEC tunnels. For example the default route is not needed by the neighbour on the end of the IPSEC tunnel, and the network between the Failover VDOM and the VDSL modem is not needed by the root VDOM.
I started by trying to block just that 10.1.2.0/24 prefix being advertised to the root VDOM at Peer ID 10.1.2551 while allowing any other prefixes to be advertised.
I had a bit of a play around with access lists as per this article: http://help.fortinet.com/fos50hlp/54/Content/FortiOS/fortigate-advanced-routing-54/Routing_BGP/Redistributing_Blocking_Routes.htm
However, I found doing so blocks all routes being advertised. I also tried the same with prefix lists and a distribute-list-out in the neighbour config and got the same result.
So.. at this point I logged a ticket with Fortinet support, and after a bit of back and forth with diagnostics etc and him sending me this link http://kb.fortinet.com/kb/viewContent.do?externalId=FD30432 and me getting the same result, I was told to contact my vendor to log a feature request.
Obviously that isn’t very helpful and I’m sure the device can do what I’m trying, so I spent a bit of time hacking away and got it with this:
# show router prefix-list
config router prefix-list
edit "block-dmz"
config rule
edit 1
set action deny
set prefix 10.1.2.0 255.255.255.0
unset ge
unset le
next
edit 2
set prefix 0.0.0.0 0.0.0.0
unset ge
set le 32
next
end
next
end
# show router route-map
config router route-map
edit "block-only-dmz"
config rule
edit 1
set match-ip-address "block-dmz"
next
end
next
end
show router bgp
config router bgp
set as 4200000001
set router-id 10.1.255.2
config neighbor
edit "10.1.255.1"
set soft-reconfiguration enable
set remote-as 4200000000
set route-map-out "block-only-dmz"
set send-community6 disable
next
end
config redistribute "connected"
set status enable
end
config redistribute "rip"
end
config redistribute "ospf"
end
config redistribute "static"
set status enable
end
config redistribute "isis"
end
config redistribute6 "connected"
end
config redistribute6 "rip"
end
config redistribute6 "ospf"
end
config redistribute6 "static"
end
config redistribute6 "isis"
end
end
So, the solution was in the prefix list. Rule 1 denies the specific subnet, but unless the rest of the IPv4 range is defined afterwards (with implicit allow) then it blocks everything.
Rule 2 uses set le 32 to match the whole IPv4 range (that isn’t previously blocked by rule 1).
Now I can apply similar rules to the IPSEC neighbours.
Hi there! I have a similar configuration that I’m trying to solve. I would like to filter out all incoming OSPF routes from my Cisco switch to the Fortigate EXCEPT for the default route. I cannot filter routes outbound on the Cisco switch so I have to filter inbound on the Fortigate. Would you say that having rule #1 be deny any and then rule #2 to allow 0.0.0.0/0.0.0.0 specifically be the way to do this?
Thanks in advance!
LikeLike
I’m sure you’ve figured this out by now, but in case not..
Since I wrote this post I stopped working with Fortigates (in fact I stopped working with networks at all) so I can’t easily test, but I think you’re right, you firstly deny 0.0.0.0/0.0.0.0 with unset ge and set le 32, then your next rule is allow 0.0.0.0/0.0.0.0 unset ge unset le to match exactly the default route. That might not be exactly right, it’s possible the deny will overlap the rule underneath and you block everything, maybe the allow comes first then the block.
Good luck.
LikeLike